Juno | ChainLight
@junorouse
Followers
1,967
Following
859
Media
213
Statuses
1,209
@chainlight_io intern, team lead. Building an essential risk management platform for Web3.
Seoul
Joined April 2019
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
Venezuela
• 2760477 Tweets
Nicolás Maduro
• 1357389 Tweets
Edmundo
• 1272332 Tweets
María Corina
• 614839 Tweets
El CNE
• 537878 Tweets
#HouseOfTheDragon
• 324830 Tweets
Chávez
• 308016 Tweets
Gala
• 281948 Tweets
Ganó Maduro
• 211306 Tweets
Robo
• 191531 Tweets
#LaCasaDeLosFamososMx
• 135801 Tweets
Rhaenyra
• 128250 Tweets
Miraflores
• 110133 Tweets
Diosdado
• 98538 Tweets
Maldito
• 88263 Tweets
Golpe de Estado
• 87256 Tweets
Vermithor
• 80762 Tweets
Boric
• 80383 Tweets
#HOTD
• 70931 Tweets
#FueraMaduro
• 60448 Tweets
Latinoamérica
• 59930 Tweets
Daemon
• 57334 Tweets
Venezolanos
• 42950 Tweets
Aemond
• 40260 Tweets
Pinochet
• 38314 Tweets
Paola
• 37587 Tweets
Vhagar
• 33238 Tweets
Cállate
• 26525 Tweets
Jace
• 25517 Tweets
Capriles
• 20064 Tweets
サザエさん
• 17247 Tweets
一粒万倍日
• 16249 Tweets
Honduras
• 15317 Tweets
山田くん
• 14222 Tweets
山本圭子さん
• 14219 Tweets
KerjaHARMONIS KerjaSELARAS
• 14049 Tweets
花沢さん
• 12590 Tweets
ちびまる子ちゃん
• 12571 Tweets
Last Seen Profiles
Pinned Tweet
gg
This effectively makes # of unsolved challenges to be 0 for The Duck :) It was a fun weekend activity that allowed Theori researchers to show off their deep knowledge and strong skills in Web3 security.
Thanks to
@paradigm_ctf
for hosting the CTF!
8
8
121
1
1
11
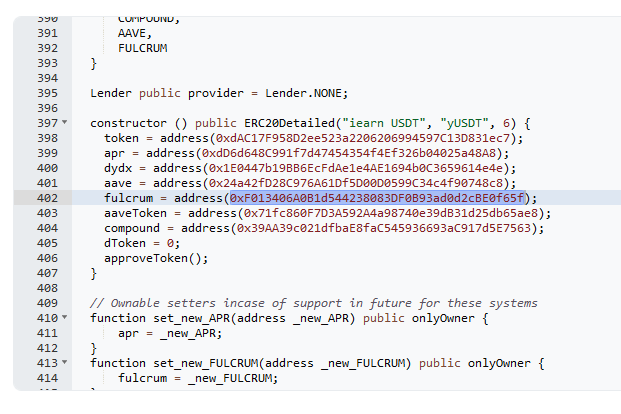
I summarized the entire exploit step.
Exploit steps:
1. Attacker repaid entire loan from aUSDT to set the borrowRate to 0.
2. Attacker minted yUSDT
3. Attacker minted iUSDC
4. Attacker sent iUSDC to yUSDT
5. yUSDT miscalculated its pool ratio (calcPoolValueInToken)
a. ROOT
3
13
63
Angry defender from Confidence 2020 CTF Write Up: also unintended solution of two rust sandbox challs in the same directory.
@t0nk42
thanks for good slide and research, it was very helpful. :D
3
17
64
Last weekend, me and
@jinmo123
took 4th place in the mev-share CTF with
@chainlight_io
.
It was fun, and I think the CTF material could be a good resource for Mevshare beginners.
There's a lot of great writing about each challenge, so I've prepared a few key takeaways 🧵
New MEV-Share CTF leaderboard is up!
Had a bit of fun coding this up last minute. Pure html/css/js 🤓 (as if anyone cares lol).
Shoutout to
@deadpine_xyz
for designing it! This my amateur implementation of her (even better-looking) design.
3
3
47
1
1
38
Our 🏋️♂️🏋️♂️🏋️♂️
2
0
30
We,
@theori_io
are making the crypto world safer!
New postmortem!
Whitehat
@junorouse
found a critical bug in
@PancakeSwap
's lottery contract, which also affected
@PantherSwap
,
@ape_swap
, and
@KnightsBsc
.
PancakeSwap paid out a big $70,000 bug bounty.
Immunefi led the disclosure process. Funds safu.
0
15
77
2
3
29
My friend, and legendary hacker
@tjbecker_x
has given up trying to recover his own
@x
account, created a new one. Follow him to learn cutting-edge hacking skills (ZK, Advanced Ethereum Knowledges, Browser pwn, etc.)
5
5
29
I uploaded the source code of our DEFCON 27 CTF exploit framework! Enjoy it.
cc.
#SeoulPlusBadass
,
@aka_saika
-- I made the front page a day before the CTF, please understand dirty codes ㅠ_ㅠ
1
8
28
Heh ZKSync bugbounty writeup was one of the big things I said
Saving $1.9B.
On September 15th, we discovered and reported a critical bug in
@zkSync
Era's ZK-Circuits that could have drained all the tokens passing through the bridge.
This bug allows a malicious prover to produce "proofs" for invalidly executed blocks, which the verifier
23
58
314
2
0
27
We are running our cutting-edge skill CTF with
@POC_Crew
.
You can get a "FREE" POC 2021 TICKET as a prize!
The challenges are based on "Real-World" vulns in the automobility systems, home IOT, Apache CVE-2021-41773, Intel AVX instruction sets, and so on. Enjoy!
🚩POC Cutting Edge CTF 현재 랭킹입니다.
CTF는 11월 6일까지 계속되니까요~ 참여하시는 #드림핵 유저님 모두 파이팅입니다👊
#POC2021
#CuttingEdge
#CTF
참여하기
➡
0
3
9
1
2
26
Head to
@TheTrustX
for some
@ChainLight_io
merch 👕 drop
Ping me if you wanna chat w me
Thanks
@bytes032
for the ticket 🤩😎
3
0
27
WE WERE ABLE TO BREAK THE ENTIRE 💎 TON NETWORK, AND WERE ONLY OFFERED "$5k" AS BOUNTY 🤯
Read our sad story ➡️
🚨 ChainLight Patch Thursday, the first week of July!
The content we introduce in this Patch Thursday is "Identifying Vulnerabilities in
#TON
: Killing All Nodes"!
✨ ChainLight has uncovered a Denial-of-Service (DoS) vulnerability in the TON network’s node that can lead to the
0
5
23
2
3
22
GM 🇹🇷
Join us at
@Hyperlane_xyz
's Modular Day tomorrow!
Our lead,
@junorouse
, will be on the Security panel with EigenLayer's
@0xkydo
, Movement's
@rushimanche
, and ETHGlobal's
@jacobwillemsma
We've prepared some limited-edition merch for our followers. FCFS.
1
2
14
0
0
21
We,
@chainlight_io
,
@tjbecker_
solved it in 2 ways.
Part 1: Reuse the signature from the previous transaction. (
@shunduquar
also mentioned)
Part 2: hash=0, r=P.x, s=P.x
Part 3: “Faketoshi Signature” from
@shunduquar
Here is the first writeup for Part 1 and Part 2 the Alpha Goat NFT CTF by auditing firm
@kebabsec
Moral of the story:
this is unsafe:
signer == bytes32(data).recover(signature);
this is safe:
signer == data.toEthSignedMessageHash().recover(signature);
1
3
30
1
4
19
Our team at
@theori_io
got 10k points from the Ethereum bug bounty program - approx. $10k in USD!
-- We will write the details as soon as possible under responsible disclosure.
0
3
21
Nice weather/ Talk/Food/AV all the things are amazing in
@summit_defi
Committee's response time in food is super fast 😋
I hope I can share my experience in web3 security next year!!
0
2
18
💪 work 24 hours a day 🏃♀️
🫡 eat pwn sleep repeat ‼️
2
0
17
gg
This may be our hardest challenge yet!
We got many questions for our December challenge - but no winner!
You still have a chance to send us a script that retrieves the flag to contact
@ssd
-disclosure.com and win a $100 Amazon gift card!
2
8
66
3
0
17
Usurper's Throne is live on
@BuildOnBase
@ChainLight_io
@osec_io
@zellic_io
The first few puzzles are ETH mainnet.
The next remaining ones will be on
@BuildOnBase
.
1
0
9
0
1
15
zz gg 수고하셨읍니다 다들, 디코가 신나서 재밌었어요 😋
w/
@5unKn0wn
@bbbig12
@wooeong337
(T코인 보고 SpaceX Rocket으로 만들었습니다 ㅎ)
2
0
14
hacklu ctf doyouevenxss exploit.
@pspaul95
says i solved some stages with unintended solution.. plz wait for official writeup!
1
3
14
🚩 How
@chainlight_io
solved the
@curta_ctf
's
#6
puzzle in a nutshell:
TL;DR: kinda meet-in-the-middle attack
1. brute-force a proper gas limit which meets "0000ABCD", the return value of the first call of gamma fn. (1/65535 opportunity)
2. another brute-force a proper
1
1
14
Happy to work for the public good.
0
0
13
I've sent a bug bounty report to
@PancakeSwap
via
@immunefi
, please have a look. BTW, i have no idea why I was banned from official telegram after submitting a report 🧐🤨
1
0
12
How was Enterprise Blockchain? It is created with
@setuid0x0_
,
@minebuu_
. Sorry for the unintended solution btw. We forgot to change sendMessage's visibility to internal. 😭
If anyone can solve it without using public sendMessage function, DM ME!
4
0
12
New audit report is coming... 🧐
Theori always do our best to protect the crypto world.
Security of your assets is our top priority.
@certik_io
and
@theori_io
are conducting
@BiFi_lending
's BTC lending smart contract security audits.
We’re in the final testing and audit phases of BTC lending, so just hang on a little bit more. We're almost there 💪
8
13
53
0
1
9
WE DO, WE WIN.
DM me if you folks want to know more about us and follow
@chainlight_io
to check out our web3 expertise.
2
0
10
Yep, we did it! I solved DTRI, DevMaster1, bnv, gLotto (with
@RBTree_Pg_
,
@adm1nkyj1
). Almost 16h+ for gLotto :(
0
0
10
DM me if you want to get an audit
Blend (blur's NFT lending platform) has been audited by
@chainlight_io
The audit report is available on the blur docs site
ChainLight is a winner of the 2022
@paradigm
CTF and has many experienced security experts
Check out:
4
3
36
0
4
10
INTERVIEW 🔥
Theori는 Web3 보안을 위해 무엇을 하고 있을까요?
#블록체인 데이터를 살피고 위험 관리를 하며 Web3 세상을 안전하게 만드는 팀입니다.
#Web3
세상을 밝게 비추는
@chainlight_io
팀 juno, mika, qwaz의 이야기,
지금 확인해 보세요!
#티오리 #인터뷰 #체인라이트
0
6
19
0
0
10