Rob Braxman Tech ⭐️⭐️⭐️
@robbraxmantech
Followers
11,944
Following
1,443
Media
348
Statuses
1,721
Alt-Tech, Subversive Nerd, Internet Privacy Guy Youtube, Odysee, Rumble Jazz Pianist
Los Angeles, CA
Joined January 2013
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
#ปิ่นภักดิ์EP10
• 832115 Tweets
TLP THE SECRET OF RING
• 820836 Tweets
凱旋門賞
• 131569 Tweets
HUNTER×HUNTER
• 104212 Tweets
Jets
• 96604 Tweets
Vikings
• 60742 Tweets
シンエンペラー
• 59250 Tweets
Lewandowski
• 58789 Tweets
Rodgers
• 55328 Tweets
宇宙戦艦ヤマト
• 51075 Tweets
中嶋監督
• 47729 Tweets
Brighton
• 36981 Tweets
ブルーストッキング
• 25707 Tweets
Saleh
• 20806 Tweets
Mertens
• 16830 Tweets
ハンターハンター
• 15839 Tweets
#GSvALN
• 15027 Tweets
アヴァンチュール
• 14554 Tweets
Ange
• 14373 Tweets
Jefferson
• 10869 Tweets
Last Seen Profiles
What the Zuck! Why is Twitter now blocking VPNs???? This is totally unacceptable! So now we cannot use Twitter in a privacy respecting manner?
@elonmusk
40
31
159
Let me restate this so it is clearer. The Intelligence Community (IC) pays Big Tech for access to control the populace, including US Citizens. In other words it is a disinformation and surveillance actor.
@snowden
already revealed this. But it persists.
12
25
76
When Law Enforcement does a dragnet search of activity in an area using Geofencing and using it to find suspects, with no warrant, affecting possibly thousands of innocents, that does not involve
#FISA
but yet it occurs often. Get a de-Googled phone and decline to participate.
4
16
62
My interview with John McAfee!
@officialmcafee
I will do a live stream on Friday 8pm Pacific on Youtube discussing and analyzing what we talked about.
2
15
56
@elonmusk
@ggreenwald
@mtaibbi
The new significance of this is that Twitter may be the only place without explicit control of 3 letter agencies! Fantastic!
3
11
54
@elonmusk
@IFNY2775
@micsolana
Legit question here. Does the Tesla send real time location information to Tesla HQ? I would like a straight and honest answer on this. This is important.
15
8
52
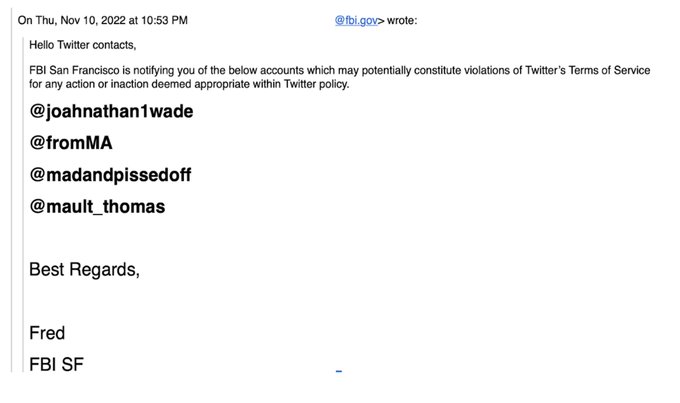
There you go. Phone weaponization. Exactly what I talk about.
6
22
50
Easy. Consider mandating that those who fear getting an infection SHOULD WEAR A MASK. The rest of us should be LEFT ALONE. That is what LA County needs to mandate.
3
2
45
What I do today for Privacy is only possible because of information I learned from Snowden and Assange. They are heroes of the people.
2
10
40
FBI pulling strings on social media is CORRUPT! I've already lived under a dictator controlling the press. ENOUGH!
3
10
37
@elonmusk
@yvanleterrible2
Well I can't sign up for Twitter Blue because it requires a zucking iPhone! I don't use those zucking devices.
2
2
37
@session_app
I will make a video supporting Session. Of the hardcore secure messengers, this hits me as the only app that actually understands the problem well.
1
2
31
While it is distressing to see congress approve
#FISA702
, are we missing the fact that digital warrantless surveillance happens without FISA? Things like geofencing for example that's been used in so many legal cases, including Jan 6.
1
10
32