Moblig
@moblig_
Followers
7K
Following
1K
Statuses
568
#1 Hacker at BugCon LHE Mexico 2021 & 2022 | Top Ranked in H1 Mexico Leaderboard 2021, 2022, 2023 | Offensive Security Engineer | Tweets are my own
127.0.0.1
Joined August 2021
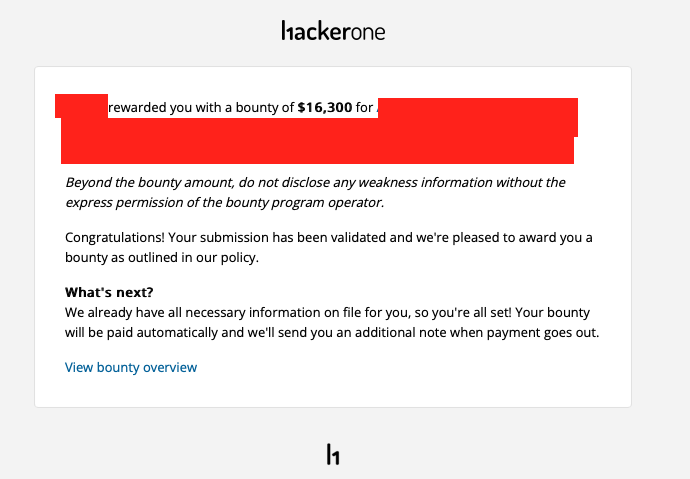
Yay, I was awarded a $16,300 bounty on @Hacker0x01! #TogetherWeHitHarder 🎉🎉🎉 Tip: Even if an asset asks for authentication, fuzz for endpoints using ffuf, I found an unauthenticated API that allowed me to retrieve sensitive information!
42
91
1K
@baraa_mansi Additional checks, I usually look into stocks in the space industry and energy sector, high growth potential, I also check their revenue streams, with that I try to determine the best time to invest
0
0
3
RT @whiteintel_io: We’re deep in development on the next version of WhiteIntel, aiming to launch in two months—assuming we can finally figu…
0
2
0
Not the first time he has been accused of scamming people
One more example for bad behavior / Scam in paid subscription for bugbounty I was there for the last 5 months trying to find something useful but unfortunately nothing , just a ready payloads and some tips filtered for each bug and this month I found a interesting script with lot of installing issues , and when I asked for help , he’s keep ignoring Nothin new in the last 5 months , so it should be one time payment payments should be 20$ and this month they took 40$ Just cancel the auto payment as Iam always trying to show everything good in bugbounty tips and sure for free, In the same time I will drop the bad content like this as well #bugbountyScam
1
1
44
RT @whiteintel_io: Hi folks Ekin from WhiteIntel here Our Co-Founder has taken off a month because "he has worked so hard this year" and…
0
1
0
RT @tbbhunter: How I Accessed Microsoft’s ServiceNow — Exposing ALL Microsoft Employee emails, Chat Support Transcripts & Attachments http…
0
13
0
RT @binitamshah: How I Accessed Microsoft’s ServiceNow — Exposing ALL Microsoft Employee emails,Chat Support Transcripts & Attachments : ht…
0
13
0
@awaisaskanii @BugCON Sorry man the team is taking a lot of time to resolve it, will publish as soon as they fix🙌🏻
0
0
1
RT @Uritechbarranco: En la @BugCON, con dos grandes ponentes y amigos! @Yess_2021xD y @moblig_, gracias por su sencillez, por compartir y m…
0
5
0