b33f | 🇺🇦✊
@FuzzySec
Followers
32,137
Following
898
Media
1,202
Statuses
9,055
意志 / Antiquarian @ IBM Adversary Services / Ex-TORE ⚔️🦅 / I rewrite pointers and read memory / AI Psychoanalyst / Teaching @CalypsoLabs
Jumanji
Joined April 2012
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
مدريد
• 1022673 Tweets
بنفيكا
• 502710 Tweets
Wizkid
• 379614 Tweets
Davido
• 342632 Tweets
Jack Smith
• 132146 Tweets
Bayern
• 113520 Tweets
Lille
• 101742 Tweets
Tigers
• 84977 Tweets
Aston Villa
• 63261 Tweets
Benfica
• 56169 Tweets
Duran
• 54682 Tweets
Mbappe
• 53708 Tweets
Astros
• 47404 Tweets
Ancelotti
• 42795 Tweets
Bank of America
• 35275 Tweets
Kerem
• 32099 Tweets
Shawn
• 30746 Tweets
Carlo
• 25514 Tweets
#ChampionsLeague
• 22476 Tweets
Camavinga
• 20835 Tweets
#LOSCRMA
• 19353 Tweets
Simeone
• 14968 Tweets
Dibu
• 12830 Tweets
Lunin
• 12723 Tweets
Jonathan David
• 11500 Tweets
Kroos
• 10973 Tweets
Rodrygo
• 10869 Tweets
Vlahovic
• 10576 Tweets
Neuer
• 10285 Tweets
Last Seen Profiles
You definitely aren't more safe on Apple than on Android. Standardized hardware/software with such a large consumer base just means that VR efforts are more focused with better ROI. I switched to an iPhone earlier this year and it's honestly terrifying that there have been like 5
45
123
922
I have posted the slides for the
#BlackHat
talk
@chompie1337
and I gave yesterday -> Close encounters of the advanced persistent kind: Leveraging rootkits for post-exploitation
16
251
700
👋 I'm releasing StandIn, a small .NET 35/45 AD post-exploitation toolkit I wrote for
@xforcered
. Hacking on endpoint is my regular jam but directory services programming is pretty 🔥🧙♂️🍩
7
254
558
I posted the slides for "Staying # and Bringing Covert Injection Tradecraft to .NET" which I presented with
@TheRealWover
at
@BlueHatIL
⚔️👻🍩 =>
8
217
469
Start-Hollow -> I POC'd up process hollowing in
#PowerShell
(x32/64), can set parent process =>
7
243
447
I wrote up a POC, WindfarmDynamite, to educate myself on process injection using WNF. This work is based on the great research by
@aionescu
/
@pwissenlit
and the awesome work by modexp ❤️👻⚔️. For further details check out the GitHub page =>
3
228
444
I'm releasing Dendrobate, a framework that can be used to generate managed code hooking payloads. I also added a small case-study on stealing MFA tokens from memory🧙♂️.
Check it out on the
@xforcered
GitHub☠️🐸 =>
6
194
429
I wrote a small tool, SwampThing, to demo command line spoofing as outlined by
@joehowwolf
in his recent talk at Wild West Hackin Fest (definitely go check that out!). Think here about uses cases like WMIC with stylesheets 🧙♂️ =>
7
224
427
I'm so excited today to announce that I'm launching my own online training platform
@CalypsoLabs
🎊
The first course to appear on Labs is "Windows Instrumentation with Frida", check it out:
Labs is partnering with
@vector35
, when you sign up you get a
42
113
418
I though I might as well drop this stand-alone port of
@tiraniddo
's UAC token abuse, bypasses "AlwaysNotify" -
8
252
367
I hope defenders have taken note of PrivExchange and kicked their Admin's into action. Don't make me come and investigate that meltdown 👻. Check out this post by
@G0ldenGunSec
-> and the execute-assembly evil by
@den_n1s
->
0
170
337
Don't think attackers can modify your event logs? Are you shipping logs off for remote collection? Have you set traps for EventLogEdit type attacks (e.g. handle duplication, thread state, file write events)? Check out my
#PowerShell
POC demo 🙈🔪💣 -
3
165
302
I added a kernel shellcode generator to the
#PowerShell
PSKernel-Primitives repo -> Get-KernelShellCode:
4
142
284
200+ RCE vulns in Trend Micro, the HITB slides are totally savage guys! 😍😎
@steventseeley
&
@malerisch
-
2
196
277
I implemented doppleganger in
#PowerShell
, still needs a bit of cleanup. Seems to do the trick but there are some limitations (x64->x32 & need write access to the process you want to masquerade).
2
120
262
A
#PowerShell
wrapper for CVE-2017-8464 LNK vulnerability is coming 😎 (uses ShellLink lib cc
@yorickkoster
)
3
151
245
I have released Fermion, an electron application for
@fridadotre
with integrated Monaco code editor. Check out the repo here => you can also download a pre-built release package for x64 Windows ❤️💀
3
94
217
I wrote an "aimbot" for XP's minesweeper (any size / configuration) using
@fridadotre
, apparently I got some high scores ❤️😂😂. POC is in the
#Fermion
repo =>
7
54
213
I posted the slides and demo's for my talk at
@WWHackinFest
Statikk Shiv: Leveraging Electron Applications For Post-Exploitation =>
12
75
213
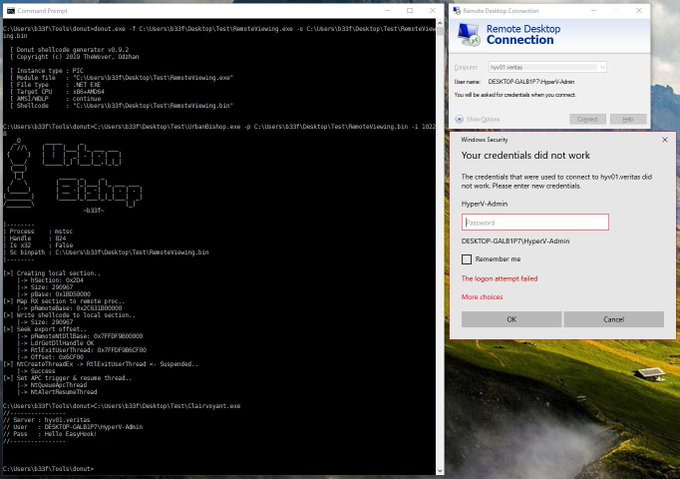
I spent some time studying Donut () recently, great work by
@TheRealWover
and odzhan <3. I wrote a small loader for testing, UrbanBishop, which is doing some interesting tricks. Details on GitHub =>
2
99
211
The recording for the talk I did at SANS HackFest is online:
(Ab)using the Microsoft Identity Platform: Exploring Azure AD Token Caching
I want to thank
@Steph3nSims
for the invitation and putting on such an excellent event 🙇♂️
5
75
208
I wanted to highlight some of the foundational capabilities that we introduced into SharpSploit as part of our
#BlueHatIL
talk --> Manual mapping, generic Syscalls & dynamic module/function resolution. Simple usage examples here =>
0
87
208
Here is an RCE demo for Cobalt Strike CVE-2022-39197. Like
@0x09AL
said the patch is not a complete fix, be careful. Also I don't want to see any more java code for a while, holy f. Maybe at some point I will post some patch analysis 🥃
17
90
195
I wrote a
#PowerShell
function, Native-HardLink to create NtSetInformationFile hard links on Windows (seems appropriate given this week 😉) =>
2
104
193
I pushed an update for
@xforcered
StandIn (v1.3) which includes a number of companion functions for Certify and ADCS template attacks 🌶️👻🧙♂️ ==> new docs
3
83
186
Tonight I'm toasting team red; may your phish always have a ring of truth, may the domain be full of silver and your tickets made of gold. I'm very exited to announce I'm hopping the fence to the blue side on
@FireEye
's Advanced Practices team 🧙♂️🔥 (Cc
@ItsReallyNick
)
30
18
183
Looking at -> Exploiting Windows RPC to bypass CFG mitigation (
@iamelli0t
)
This indirection using NdrServerCall2 is really interesting (not just for VR). I wrote a small Frida script for parsing:
3
58
179
Over the weekend I was reading a post by
@inversecos
on exploiting an Arm64 binary:
I thought it would be interesting to also do the exploit on x64 Windows and show how we can use Frida to autopwn the binary, check it out on 🔪🧥
2
63
172
Wait but why does Windows let you load a driver that was signed with a cert which is now expired and was not timestamped when it was signed? How does that make sense (cc
@mattifestation
)? I recommend that defenders write signatures for files signed with leaked NVIDIA certificate
14
25
157
A quick demo of corrupting an IORING object for arbitrary R/W on Win11 22H2+. Big thanks to
@yarden_shafir
for her excellent research and debugging help 😁💐. Probably I will write a small overview of the process on 🔪🧥 later this week.
3
38
150
Low integrity token stealing on Win10 RS2, I will update the
#PowerShell
PSKernel-Primitives repo tomorrow! (cc
@Blomster81
)
2
78
145
Check out this great talk by
@Cyb3rWard0g
&
@cyb3rPandah
at Insomni'hack => If you play with SilkETW remember that you can augment your collection with Yara and only write matches to file/ELK/eventlog ❤️🔪
1
63
148
TyphoonCon 2019: Overview of the latest Windows OS kernel exploits found in the wild (
@oct0xor
&
@0x1ffffffffffff
) =>
2
74
142
Because online dating is harder than any FromSoft boss I decided to spend a little bit of time today on making a not-really-submission for the Binary Golf
#BGGP4
replicate challenge using .NET PE's. You can read the write-up here:
1
43
142