T. M໐ri
@valdzone
Followers
1,231
Following
565
Media
1,021
Statuses
10,187
大学で研究+教員をしています。研究の興味は人工知能や自動運転など新しいテクノロジのセキュリティです。未来の技術を人間がどのように利用、あるいは悪用するかに強い興味・関心があります。ツイートは本人が普段考えている雑多な事柄を、意図的あるいは非意図的に漏洩するための「サイドチャネル」です。ホモグリフを見かけると喜びます。
Joined April 2007
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
BTS BTS BTS
• 353264 Tweets
RENJUN
• 339848 Tweets
Steelers
• 127810 Tweets
Dodgers
• 78922 Tweets
Cowboys
• 77268 Tweets
Fields
• 65979 Tweets
Chilpancingo
• 51776 Tweets
斉藤慎二
• 47319 Tweets
リポストキャンペーン開催中
• 45933 Tweets
書類送検
• 42112 Tweets
斉藤メンバー
• 39918 Tweets
#FinalLaAcademia
• 39027 Tweets
ジャングルポケット
• 37523 Tweets
BTS PAVED THE WAY
• 36228 Tweets
Pittsburgh
• 33510 Tweets
ジャンポケ斉藤
• 24072 Tweets
ロケバス
• 22278 Tweets
体調不良
• 20773 Tweets
ダルビッシュ
• 18990 Tweets
#ドミノでトリックオアチーズ
• 18423 Tweets
斉藤さん
• 15269 Tweets
PrabowoJKW SolidKOMPAK
• 14244 Tweets
NKRItangguh KOKOHdisegani
• 13526 Tweets
Dak Prescott
• 13339 Tweets
性的暴行
• 13023 Tweets
pickens
• 12310 Tweets
Last Seen Profiles
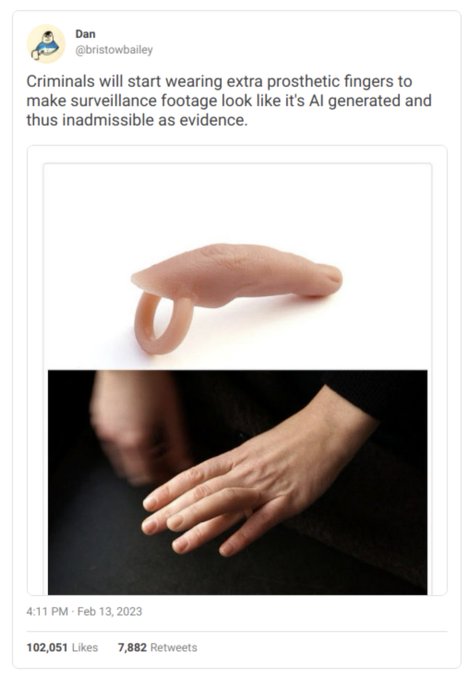
この論文は、Facebook が2要素認証のために必要だということで取得したユーザの電話番号等を、実は裏ではターゲット広告のために使っていたことを明らかにしたという話。
2
847
827
論文の最初の1文は、論文に入魂するためにある。
下記はUSENIX SECの論文379本を対象に、最初の1文を調査した結果。これは面白い!
事実の説明や、トピックの適合性から入るものが多いとのこと。
作者らによるTop 5 favoritesの選を見ると、最初の1文だけで、読む価値がある論文だと思わされる。
Good writing is hard for academics.
For fun,
@demirag_d
and I studied 379 USENIX Security papers, focusing on the opening sentence. How do authors try to hook the reader?
Full write-up:
Thread: ⬇️
5
83
282
1
25
96
科研申請書から罫線がなくなったのは
@konotarogomame
氏のおかげと思われるのだけど(科研費LaTeXユーザとしては困ってなかったけど)、氏の情処会誌への寄稿
状況を変えたかったら研究者から政治家の輩出を、というのは正論。
2
77
73
なるほど、LLMがハルシネーションで存在しないライブラリを勧めてくるのを狙って、予めその名前空間に悪いものを仕込んでおくと
1
21
50
(やや旧聞となりますが)研究室卒業生の松尾君が Black Hat USA で研究成果を発表しました!
本研究は、彼の在学時に
@FFRI_Research
との共同研究として実施したもので、ご指導頂いたFFRI中川さん、茂木さんに感謝いたします
0
4
40
@OLIET_lab
脅威の実現性を示したのはとても重要な事ですが、実サービスを対象に攻撃できること、その手順を責任ある情報開示のプロセスを経ずに公開してしまう事は問題です(悪用されるリスク)
決済が絡んでいることもあり、訴訟リスクもありますので、至急JPCERT/CC、関係各社に相談することをおすすめします
0
3
37
研究室学生の論文が best paper award を受賞!NTTとの共同研究成果です。
🥳🏆 Congratulations🏆 👏
The paper "Careless Participants Are Essential For Our
#Phishing
Study: Understanding the Impact of Screening Methods" by T. Matsuura, A. Hasegawa, M. Akiyama and T. Mori was honored as the best paper at this year's
#EuroUSEC2021
.
1
6
20
1
6
37