Tenset Security
@tenset_security
Followers
2,680
Following
140
Media
37
Statuses
481
Follow for tips on how to protect your crypto project.
Joined June 2023
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
Eagles
• 125522 Tweets
Dick Cheney
• 121685 Tweets
Uruguay
• 48154 Tweets
Peacock
• 38075 Tweets
Jalen
• 27583 Tweets
#SmackDown
• 26222 Tweets
Paraguay
• 25341 Tweets
Alan Dershowitz
• 22358 Tweets
Go Birds
• 22022 Tweets
Green Bay
• 18519 Tweets
FELIX NEW YORK FASHION WEEK
• 17339 Tweets
#GoPackGo
• 12432 Tweets
#GBvsPHI
• 12273 Tweets
Saquon
• 11320 Tweets
Vinci
• 10331 Tweets
Last Seen Profiles
Delighted to announce we've successfully completed a comprehensive audit for
@4catamoto
's smart contracts! Thrilled to be supporting the safety & reliability of new projects on the
@BNBCHAIN
as official security service providers.
11
54
177
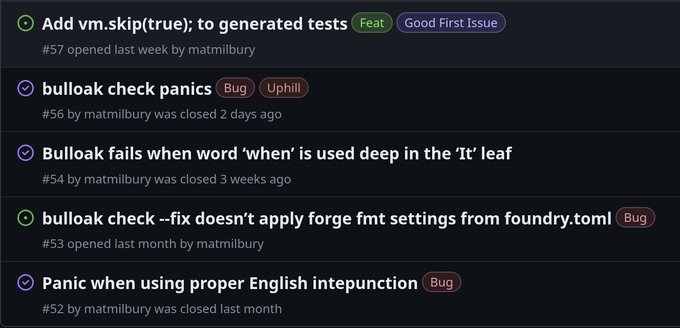
We’ve used Bulloak (an OpenSource smart contracts testing tool developed by
@OpenZeppelin
’s engineer,
@alexfertel
) extensively for the last few weeks.
Results?
4 bug reports and 1 improvement suggestion 🫡
1
14
53
Legendary
@adrianhetman
gets on stage on Defi Security Summit in a few minutes to reveal the behind the scenes of Bug Bounty triaging.
We'll be tweeting key takeaways live 👇
39
47
70
Delighted to announce we've successfully completed a comprehensive audit for
@theluckylemu
's smart contracts!
4
19
71
Excited to unveil our year-long collaboration with
@NativMetaverse
! We are working hard to develop all technical aspects of their project, providing innovative solutions every step of the way. Stay tuned for more updates!
0
6
22
Deploying smart contract upgrades though
@safe
with a Foundry script WHILE being able to write tests for that upgrade script on a mainnet fork is harder than it should be.
Yet, it's essential for all projects with upgradeable smart contracts.
We're dropping a guide soon.
0
18
32
Nobody is immune
3
6
20
Did you know? 💡
@AlgoFoundation
will double your bug bounty on chosen Algorand projects on
@immunefi
$200k -> $400k 💰
Sounds like an opportunity to go outside your comfort zone and engage in some juicy hunting 🕵️♂️🔍
2
0
24