Shodan
@shodanhq
Followers
102,546
Following
2
Media
315
Statuses
2,726
Monitor your external network, search the Internet of Things and perform empirical market research. You can also find us on
Seattle, WA
Joined January 2011
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
オリンピック
• 580311 Tweets
Christians
• 280871 Tweets
Christianity
• 202751 Tweets
花火大会
• 169328 Tweets
グラブル
• 60281 Tweets
Endrick
• 52643 Tweets
#男子バレー
• 45302 Tweets
バレー男子
• 35812 Tweets
NuNew Sing With Piano
• 28093 Tweets
#アークナイツハニバ2024
• 25608 Tweets
#withMUSIC
• 21358 Tweets
フルセット
• 14061 Tweets
#ドッキリGP
• 13842 Tweets
フォード
• 10196 Tweets
ヤスアキ
• 10181 Tweets
Last Seen Profiles
10 years ago
@achillean
launched the Shodan website! To celebrate a decade of discovery and growth we're going to offer the membership for $1 (marked down from $49) for the next 24 hours (0:00 UTC to 24:00 UTC):
156
2K
3K
Great introduction to Shodan by
@TomLawrenceTech
that discusses how it works and shares a few tips to get started:
0
54
148
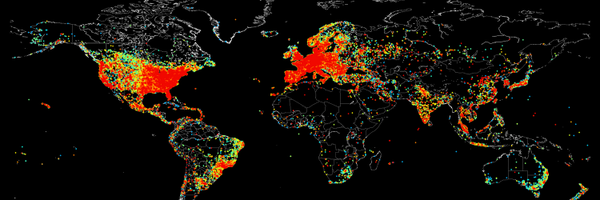
We've added JARM fingerprinting and with it introduce a new "ssl.jarm" property/ filter/ facet. Here's a breakdown of the current values for JARM fingerprints in Shodan: (h/t
@4A4133
and
@SalesforceEng
)
0
46
128
@harguilar
@achillean
it's a one-time payment for a lifetime account upgrade. there's no subscription
5
6
125
Want to query Shodan like it's a SQL database? Check out the new Steampipe integration:

Shodan Plugin for Steampipe
Query Shodan with SQL! Open source CLI. No DB required.
hub.steampipe.io
1
22
121