Dan Guido
@dguido
Followers
24,684
Following
907
Media
550
Statuses
10,432
CEO @trailofbits , organizer @EmpireHacking
Brooklyn, NY
Joined April 2008
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
Black
• 1769504 Tweets
La OEA
• 723260 Tweets
NABJ
• 534817 Tweets
Perú
• 371979 Tweets
Petro
• 347354 Tweets
Flamengo
• 232685 Tweets
Rachel Scott
• 95702 Tweets
Jamaican
• 64491 Tweets
O Palmeiras
• 57971 Tweets
Abel
• 45806 Tweets
#ทางรัฐ
• 39909 Tweets
Wesley
• 31019 Tweets
Rony
• 25861 Tweets
#FLAxPAL
• 23741 Tweets
Rojas
• 23505 Tweets
#AEWDynamite
• 23005 Tweets
Luiz Araújo
• 21254 Tweets
Paiva
• 20341 Tweets
Maracanã
• 19339 Tweets
Lavia
• 15088 Tweets
Nkunku
• 14338 Tweets
Gerson
• 13083 Tweets
O Vasco
• 12828 Tweets
無課金おじさん
• 12344 Tweets
Veiga
• 11559 Tweets
Cavani
• 10888 Tweets
Madueke
• 10696 Tweets
Last Seen Profiles
I filled out a report at the precinct, and my two patrolmen get a parade of high fives from their peers. No one can remember the last time they solved an e-bike crime! I teach them all how to use Airtags, then hop in a Lyft home.
@NinebotGlobal
agrees to RMA the scooter ♥️.
19
44
2K
1. You can't "pass" a security audit
2. You can't pentest an app secure
3. It's not independent if you paid for it
4. You should advise clients to say otherwise
See the
@trailofbits
guidelines for public citations of our work:
NordPass, as a password managing service, has successfully passed an independent
#security
#audit
by
@cure53berlin
3
3
14
11
76
370
This company is going to use photos and video from
@BlackHatEvents
to legitimize themselves for months. Blackhat should exercise copyright over their logo to take it all down.
12
73
355
I didn’t plan it this way, but rather than send a single person to RSA,
@trailofbits
sent 60 employees and their SOs to a retreat at the Whistler/Blackcomb ski resort this whole week.
7
11
289
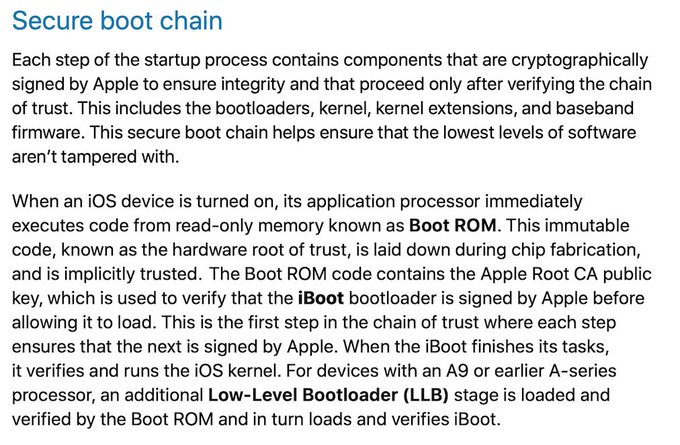
Trail of Bits has an iOS security toolkit out today: iVerify. Grab it from the app store here:
Read about it in
@Motherboard
:
and the
@trailofbits
blog:
9
96
240
This is, without a doubt, the best attempt I've seen to review VPN service providers.
5
80
238
We re-read 23 smart contract audits and found:
- 78% of high impact, easily exploitable findings are discoverable with automated analysis tools
- 50% of all findings will never be found with automated tools
- Unit testing _has no impact on security_
3
87
228
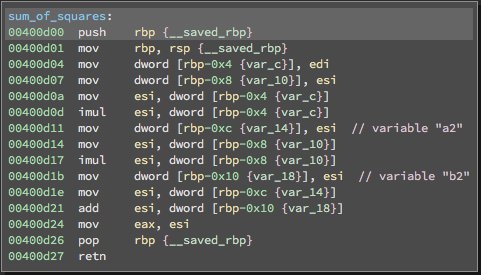
Here's the Solidity bug that lost ~$30MM in ETH today (from the
@trailofbits
internal chat)
6
153
204
We're hired to provide industry-best advice
@trailofbits
, and that's exactly what we provided to
@HegicOptions
. How, then, were bugs found in their code mere hours after they deployed it to mainnet? (1/n)
9
61
201
This week
@trailofbits
✅Released an e2e group chat library
✅Tore down 2 counterfeit phones
✅Reviewed 23 smart contract audits
✅Reported 51 Kubernetes vulns
✅Delivered 0 talks @ BH
4
35
164
Nearly all code for Bulletproofs, PlonK, and Girault’s proof of knowledge (crucial for zero knowledge proofs) were broken due to insecure randomness, recommended in the original academic papers for them. Rekt!
3
27
149
I told
@ConsumerReports
what people needed to hear about password managers: any use is better than no use.
6
85
140
Phew!
@trailofbits
is 48 employees (42 engineers), and 59 if you count summer interns. I don't know how we hold this ship together some days.
15
1
137
The embargo has been lifted!
@GeminiDotCom
is launching a US regulator-approved, fiat-collateralized, ERC20 stablecoin: the Gemini dollar. I’m pleased to announce that
@trailofbits
completed a security review of it. You can find our public report here:
3
35
125
It’s now been a week, and we still haven’t received an explanation nor do we expect to! Even if it were explained, this behavior is unacceptable for any cloud service and truly malicious for a cloud security company. cc
@badthingsdaily
3
9
124
When you hire
@trailofbits
, you typically get innovative automated security tests back. We've systematized this process internally, and are now sharing it publicly.
Here's how we use
@semgrep
for great results, quickly:
1
15
109
From maintaining Slither alone,
@trailofbits
impact on blockchain security since 2017 is pretty dramatically large. If we win this silly poll, we'll make it even larger by open-sourcing 5 of our private detectors for everyone to use. ☺️
9
12
99
Most people are now aware that
@trailofbits
conducted a security review of the Bitcoin Cash client on behalf of
@BitcoinSVNode
. While we cannot release our report in its entirety yet, I wanted to share a few details of what we found…
7
30
88
Writing security tests for clients is a big part of the future of
@trailofbits
. First blockchain, then CodeQL, Semgrep, AFL++, and more! Keep an eye on the Automated Testing Handbook for previews... ()
7
14
86
The best tool from Microsoft you're probably not using yet: BinScope, the binary analyzer
http://t.co/JaDkI99hUS
1
47
85
Yan saved the company from the brink of failure in 2013, built the foundation for our research practice, and spearheaded the development of one of our core technologies. It was a privilege to work with him.
After 6.5 years, today was my last day at
@trailofbits
. Extremely thankful for the opportunities I had with such an amazing team.
8
4
111
0
6
86
Intern projects released this week
@trailofbits
:
✅Designed a featureful, high performance C++ SQLite wrapper
✅Automated analysis of crashes from KRF with Binary Ninja
✅Ported KLEE to work on binary code
0
35
86
I adopted a dog from
@koreank9rescue
this weekend! She's a 5-month old Jindo mix with tiger stripes. What should I name her?
20
1
78
.
@trailofbits
reviewed the Voatz mobile, blockchain voting system used in real elections in Colorado, Utah, Oregon, and West Virginia. We published the report in full today, with 79 security issues identified.
2
32
75
If you want
@trailofbits
to offensively hack things in public, you can now submit "adversarial audit" projects to the OTF for us. 🤠
1
19
76
At
@trailofbits
, the standard for knowing you’re in trouble has been Googling a question and finding 1 result: a mailing list post from yourself asking the exact same question 4 years ago.
0
6
71
I'm staffing up our DARPA AIxCC team! You'll have full access to the team and resources
@trailofbits
, and join our existing stellar team to compete and win.
1
23
70
Here’s me wrapping up my lesson on computer architecture and software exploits to a class at my old high school. I take one day off every year to spend time teaching.
Great visit today from Mineola alum and
@trailofbits
CEO
@dguido
discussing cyber security, exploitations and the little man computer with our
@C2C_QCC
juniors.
#MineolaProud
0
2
11
3
0
74
Hunt for bugs in binaries with advanced static analysis techniques. In this post, Josh reliably finds Heartbleed-type bugs without access to source code.
0
26
69
SEAL is making hack back happen on the blockchain, now shipping a legal defense fund for in-scope attempts to intercept and return stolen funds
1
29
75
Periodic reminder that NYC has a mature, vibrant security ecosystem. There are dozens of startups, teams, investors, and events, and I'm proud
@trailofbits
is among them. Browse through the full listing here:
5
16
70
✅ spin a company out of
@trailofbits
🎉🎉 Big news -- iVerify is leaving the nest!After incubating at
@trailofbits
, we're setting out on our own to become the first mobile threat hunting company dedicated to rooting out mobile spyware without compromising privacy!
1
12
33
8
2
69