c0m0r1
@c0m0r1
Followers
1,740
Following
270
Media
1,001
Statuses
6,111
KAIST CS & EE 18 + EE M.S. Student 23 / KAIST GoN 18 / pwn, rev / newbie forever / 음악듣는 코모리 @DC0m0r1
Joined April 2019
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
Rosé
• 529795 Tweets
西田敏行さん
• 344228 Tweets
Sinwar
• 246142 Tweets
Bluesky
• 206331 Tweets
ブルスカ
• 193931 Tweets
スーパームーン
• 179640 Tweets
ブルースカイ
• 176888 Tweets
#わたしの宝物
• 176305 Tweets
ツイッター
• 142787 Tweets
JOURNEY CONCEPT PHOTO
• 114999 Tweets
タイッツー
• 87856 Tweets
インスタ
• 85280 Tweets
Kabir Is God
• 84879 Tweets
EFM X JACK AND JOKER
• 76993 Tweets
ILL BE THERE IN 7 DAYS
• 71922 Tweets
ログイン
• 62545 Tweets
#يحيي_السنوار
• 60240 Tweets
블루스카이
• 55705 Tweets
LINGLING MYCHERIE AMOUR EP9
• 38335 Tweets
ALRIGHT TPOP STAGE
• 27602 Tweets
#まふまふ誕生祭2024
• 21957 Tweets
غير مدبر
• 19794 Tweets
冬月くん
• 18627 Tweets
RADWIMPS
• 18246 Tweets
#TOBE緊急生配信
• 16831 Tweets
ミスキー
• 15196 Tweets
ふっかさん
• 14419 Tweets
個人サイト
• 13380 Tweets
mixi
• 11155 Tweets
ابو ابراهيم
• 10601 Tweets
Last Seen Profiles
今回
@Hommarju
先生、
@tpazolite
先生、
@ginkiha
先生に
E-amusement pass、juicy fruitsのCD、学校名ファイルへ サインを受けました!
そして合弁アルバム「CROSSING DELTA」まで...!
大切にします! ありがとうございます!
0
3
10
2022 Fall GoN Open Qual CTF가 긴 여정 끝에 막을 내렸습니다!
Zero Gravity, Bomblab - Hard, pprintable, Obstacle, Exploit Tycoon, Checkers를 출제했습니다.
고생하신 출제자 분들, 본 대회를 후원해주신 KAIST GSIS &
@CSRC_KAIST
,
@dreamhack_io
, 그리고 모든 참가자분들께 감사드립니다!
2022 Fall GoN Open Qual CTF ended. I hope you enjoyed my challenges, baby-hexagon (Pwn) & dlmalloc (Pwn). Thank you to our participants, GoN members, and our sponsors, KAIST GSIS &
@CSRC_KAIST
!
0
3
10
1
1
9
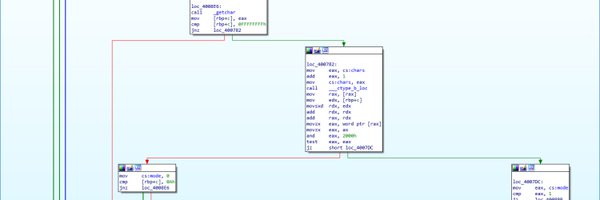
Codegate2020에 리버싱 문제 malicious를 출제했습니다.
첫 ctf 문제출제라 미숙한 점이 많았지만 재밌게 즐겨주셨다면 감사하겠습니다.
모두들 대회 수고하셨습니다!!
#codegate2020
#codegatectf
0
2
6