briankrebs
@briankrebs
Followers
344,999
Following
1,793
Media
840
Statuses
17,187
Independent investigative journalist. Author of 'Spam Nation,' a NYT bestseller. Former Washington Post reporter. Mastodon:
krebsonsecurity @ gmail.com
Joined March 2009
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
Iran
• 1068545 Tweets
إيران
• 528956 Tweets
Dodgers
• 315229 Tweets
Hybe
• 272892 Tweets
開催中のガチャ
• 155017 Tweets
中野家の五つ子のうち1体
• 144317 Tweets
期日前投票
• 142767 Tweets
#咲き誇るみこち
• 137240 Tweets
علي ايران
• 116065 Tweets
ANIM NA TAONG SAMAHAN
• 113394 Tweets
フリーマン
• 107292 Tweets
GULF FANMEETING THE FANS
• 65437 Tweets
満塁ホームラン
• 62343 Tweets
Kohli
• 54007 Tweets
Rohit
• 52567 Tweets
MERZ EXPO X PEAKMINT
• 43132 Tweets
KARAN VEER WINNING HEARTS
• 30231 Tweets
#WOWOWESTꓸやねん
• 20655 Tweets
カボチャ
• 19434 Tweets
#アークナイツ秋感謝祭2024
• 18307 Tweets
スワンS
• 15722 Tweets
キョダイマックス
• 13741 Tweets
#SMBC日本シリーズ
• 13671 Tweets
WO AI NI JIMMYSEA
• 13117 Tweets
コンパス
• 10945 Tweets
Last Seen Profiles
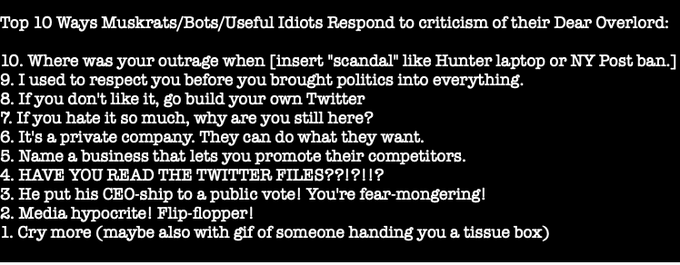
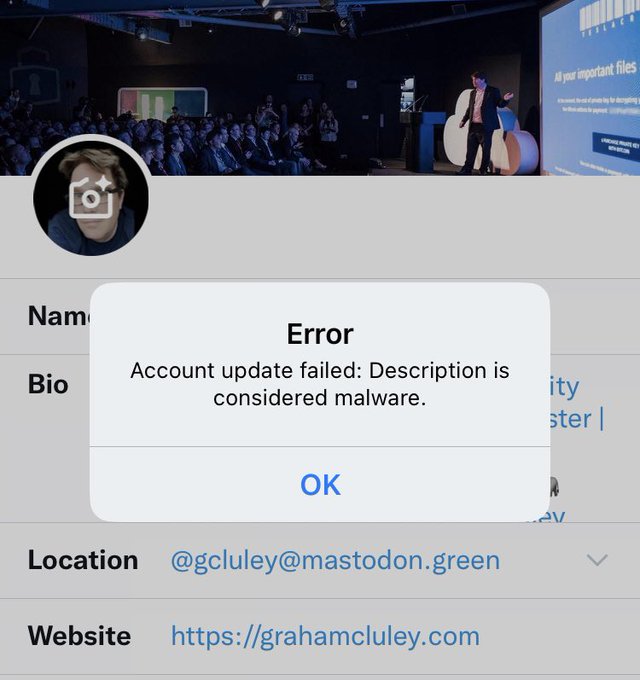
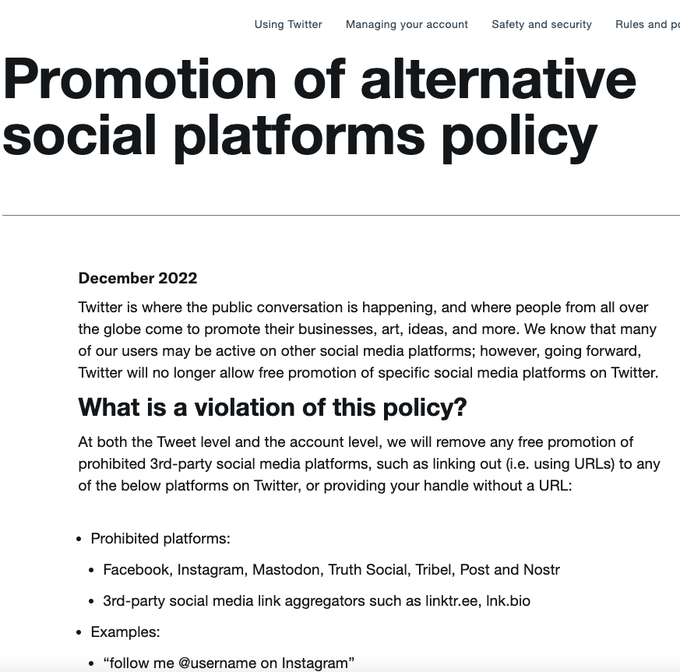
Let this sink in:
@elonmusk
hath decreed that all links to Mastodon should be flagged as malware. This is, of course, a baldfaced lie, and he knows it. So the CEO of Twitter is lying to everyone on Twitter, and to all its advertisers, even to all of his defenders.
1K
6K
21K
Everything that
@elonmusk
has done publicly so far to Twitter seems like exactly what I'd do if I wanted to ensure the entire platform ran straight into the ground, and fast. His actions and words make it really hard to see how this isn't actually his plan.
1K
3K
18K
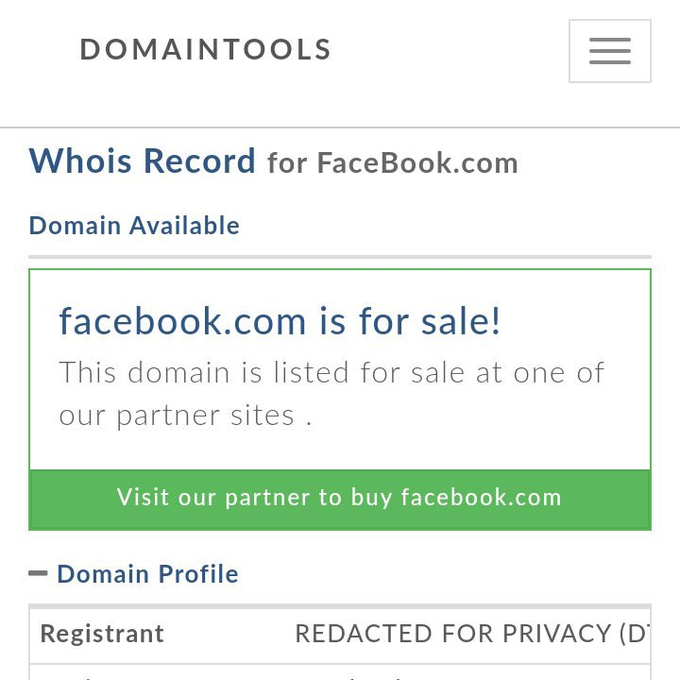
To be more precise (and Geek Factor 5) the BGP routes serving Facebook's authoritative DNS were withdrawn, rendering all Facebook domains inaccessible. That's per
@DougMadory
, who knows a few things about BGP/DNS.
99
1K
6K
Just published a short (hopefully broadly accessible) writeup on the ongoing outages at Facebook, Instagram & WhatsApp. Includes perspective, graphic from
@dougmadory
and Kentik. Will update to add more info soon.
104
2K
3K
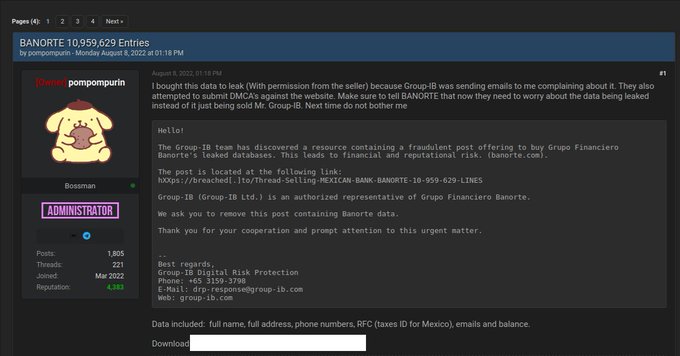
Hey
@elonmusk
, since you don't seem to have much a media/comms team anymore, can you address the apparently legitimate claim that someone scraped & is now selling data on hundreds of millions of Twitter accounts? Maybe it didn't happen on your watch, but you owe Twitter a reply.
66
429
2K
The security researcher who originally reported the
@panerabread
security vuln that exposed millions of customers' private info has just penned this response to the company's unbelievable response to my story. worth a read:
35
1K
1K
Potentially huge scoop from Bloomberg alleging San Jose-based Super Micro, under direction or control of Chinese cyber spies, secretly embedded rice-sized computer chips on electronic components stitched into devices made by 30 companies
#supplychain
79
1K
1K
Holy moly. Prolexic reports my site was just hit with the largest DDOS the internet has ever seen. 665 Gbps. Site's still up.
#FAIL
58
668
991
#1
of who knows how many in re: Why I don't go to RSAcon anymore. I always say the best way to experience RSA is not to go to any of the talks, but instead hang out at the bars near the con to let people get liquored up and tell you things they shouldn't.
35
100
873
On Monday, KrebsOnSecurity began following up on info provided by
@holdsecurity
that a ransomware group (Ryuk) is preparing to encrypt systems at possibly hundreds of medical centers/hospitals. FBI/CISA/HHS just had a call warning of "imminent, credible threat to US hospitals."
41
543
851
At the risk of making my job harder (or possibly, easier?) it's clear I'm going to have to write an entire series of blog posts about how not to handle a data breach from a PR perspective. I'm sputtering over here. Gave
@panerabread
every courtesy and they treat me like an idiot
41
195
797
Exclusive: Multiple sources now say Indian IT outsourcing giant
@Wipro
is in the throes of dealing with a months-long breach in which intruders were seen using the company's networks to attack and probe customer systems
24
808
794
Oh look,the guy my source initially notified at
@panerabread
EIGHT MONTHS AGO -- their dir. of info security - was senior dir. of security operations at Equifax until 2013. Shocker.
37
367
752