Dr. Dave Venable
@davevenable
Followers
11,203
Following
8,821
Media
480
Statuses
4,608
OPSEC Connoisseur ∙ Disinformation ∙ CISO ∙ @TheCipherBrief | Ex USIC, NSA CNE, StateDept | Book & Art Collector
Joined May 2011
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
jungkook
• 1042893 Tweets
Arsenal
• 591464 Tweets
#HAPPYJKDAY
• 403697 Tweets
#خلصوا_صفقات_الهلال2
• 385659 Tweets
برشلونه
• 214654 Tweets
بلد الوليد
• 197197 Tweets
بورنموث
• 189555 Tweets
Rice
• 165127 Tweets
Georgia
• 136784 Tweets
Brighton
• 108190 Tweets
#SixTONESANN
• 93060 Tweets
Everton
• 75165 Tweets
Raphinha
• 57792 Tweets
Lamine
• 52197 Tweets
Fatman Scoop
• 46821 Tweets
Valladolid
• 33851 Tweets
Bournemouth
• 29453 Tweets
Hansi Flick
• 29193 Tweets
McLaren
• 27789 Tweets
Iowa
• 20439 Tweets
Clemson
• 20160 Tweets
Veltman
• 18328 Tweets
エネルギー補給
• 17720 Tweets
#الاتحاد_الاحق_بالدعم1
• 17382 Tweets
Cubarsi
• 17227 Tweets
West Virginia
• 14495 Tweets
飛び降り
• 13328 Tweets
Xavi
• 13307 Tweets
West Ham
• 13240 Tweets
All Blacks
• 13180 Tweets
Red Bull
• 12997 Tweets
#RSAvNZL
• 12893 Tweets
Penn State
• 12793 Tweets
Last Seen Profiles
Pinned Tweet
Very honored to be included in
@TribeOfHackers
Blue Team. Thanks so much to
@marcusjcarey
and
@jen_jin
, I can’t wait to sit down and read the whole book! I’ve loved and learned a lot from every edition of the
#TribeOfHackers
series!
15
21
276
How to make accurate predictions:
(1) Assume the tech ends up getting to wherever you think it will;
(2) Imagine the absolute worst possible implementation of it in a genie’s curse sort of way.
From what I can tell, this will 𝘢𝘭𝘸𝘢𝘺𝘴 end up accurate.
4
28
101
Wow, this is insane:
#FunFactFriday
- The Royal Navy has been testing Jet Suit assault teams to determine if the Iron Man-like suits could be used to rapidly swarm and board ships. U.S. Special Operations Command is also evaluating a jetpack that can reach speeds of more than 200 mph.
193
1K
3K
2
27
85
Jake’s not wrong. It’s just… annoying that he’s not wrong.
I spend so much time lately defending the IC from kooky conspiracy theorists that my default reaction when I saw this yesterday was basically “c’mon now, we both know firsthand…”
But the facts are the facts. It’s
2
3
54
@RayRedacted
The big question is whether it’s due to firings, or (more likely) security is suddenly getting the budget it’s been asking for (now that it’s too late).
4
0
49
Could someone from
@BostonDynamics
please send one of your terminators back in time to prevent agile meetings from being called “ceremonies?”
4
11
44
@cmclymer
For us, bedtime was at X o’clock… but once in bed, we could read for 30 minutes if we chose to.
2
0
29
@MalwareJake
I feel like for-profit medical insurance is the bigger mistake. Co-op insurance would be so much better
2
0
30
This is the future. We’re going to see more and more operational independence and self-financing as we move forward. And with heavily sanctioned states, we’ll see more frequent use of cryptocurrency as a means to circumvent these sanctions.
2
9
26
Dear
@Apple
, if my AirPods Max have been in this position a few rooms away for the last 20+ hours, the chances of me wanting that incoming call’s audio being sent to them is ~0%.
1
1
21
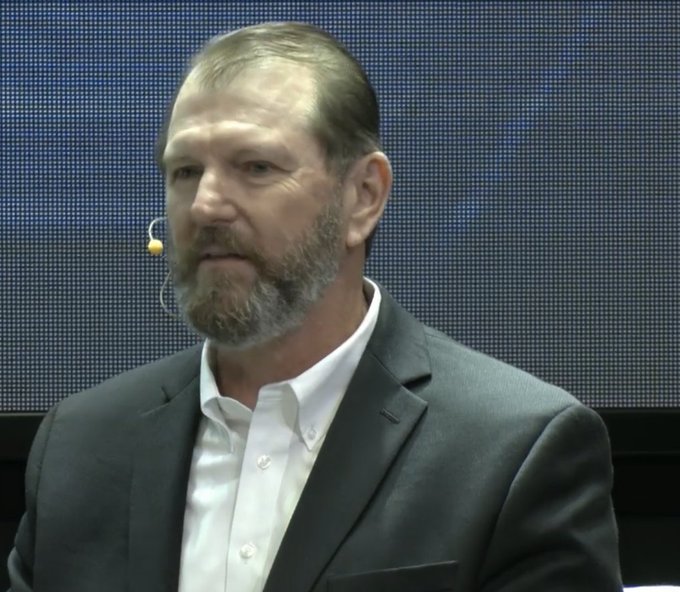
Standing room only to hear from
@PowerVertical
&
@MargoGontar
on information warfare.
#WSF2016
@StopFakingNews
0
11
19
Congrats to New Security Leaders of
@WarsawForum
! Honored to mentor this fantastic group w/
@PowerVertical
&
@BAMcCown
#WSF2016
#WSF_NSL2016
1
9
19
@rayjwatson
@HydeNS33k
@VinceintheBay
Prank of the week right here. It just calls Time & Temperature 😂
2
3
18
Impromptu
#cigarcon
with
@AllTheCybers
@RayRedacted
@R0gueG0pher
@da5ch0
@0xIntern
@_sn0ww
@FrankMcG
@cillic
4
3
18
@ercwl
@SchmiegSophie
@SoatokDhole
| ̄ ̄ ̄ ̄ ̄ ̄ ̄ ̄ ̄ ̄|
| CRYPTO |
| MEANS |
| CRYPTOZOOLOGY |
|__________|
(\__/) ||
(•ㅅ•) ||
/ づ
2
1
17
Fantastic points brought up by
@PowerVertical
and
@General_Ben
. It’s time we change the way we look at this:
What does America actually get from
@NATO
? In the second episode of CEPA's
#RoadWarrior
series,
@General_Ben
Hodges joins
@PowerVertical
to examine if the Alliance benefits the United States. Watch:
1
8
16
0
5
16
Fantastic analysis by
@EdwardLucas
at
@cepa
: finance is the next battleground for western security
Western security planners need to start preparing for what’s on the horizon, argues
@EdwardLucas
.
#EuropesEdge
0
14
17
2
8
16
.
@arrington
On the plus side, when the raid arrives they can just shout "Alexa, unlock the front door" instead of kicking it in.
0
2
15
All these "how to prevent
#wannacry
" webinars this week... Srsly? How does it take an hour to say:
1. Patch
2. Backup
3. Block dumb ports
1
8
12
@rayjwatson
@HydeNS33k
@VinceintheBay
And the "access code" spells "sucker" on the telephone keypad 😂😂😂
1
2
15
@realkimstover
They tried. We never cared (or even noticed in most cases)... then they went after Millennials and GenZ, and both groups reacted in exactly the ways that the bullies were hoping for, so they keep doing it. 🤷🏻♂️
0
0
13
The story behind this is that Radia Perlman, the “mother of the Internet,” said this to me back in like 2001. A few years ago,
@RayRedacted
and I printed it up on t-shirts and passed them out at Black Hat and DEFCON.
1
3
15
Another amazing year at the
@WarsawForum
! Congrats to my friends
@Pisarski
and
@KPisarska
on another huge success. A lot of great discussion that will lead to action. Check out this great summary video (and see me at the end!):
0
5
14
Duke’s a huge fan of the original Applied Cryptography!
For 24 hrs, for every RT including a picture of your dog & an infosec book I'll donate $5 in your name to
@DianaInitiative
, a conference focused on Women, Diversity, & Inclusion in Information Security, embracing all genders, sexualities & skill levels.
Each photo RT=$5. Go!
46
102
284
1
2
14
Ah yes, because it would totally make sense for a country/service to blow the fact that they’ve successfully defeated modulo-reduced / differential log-reduced algorithms over… VPN traffic. lmao
At Mike Lindell's cyber-security summit, this "data scientist" just told attendess not to use
@ExpressVPN
because it is (allegedly) Chinese-owned and they are allegedly using Quantum Computing to snoop on your traffic.
News flash: VPN providers don't need QC to track traffic.
66
129
799
2
1
15
Put simply, Flynn just isn’t savvy enough to be Q. 🙃
And frankly, that’s not setting a very high bar.
0
5
11
Not to mention a shift toward cyber-enabled HUMINT, which is literally just traditional HUMINT.
0
4
13
@MalwareJake
Dork is just the perfect description. Anyone that’s ever had to carry, hates carrying. It’s such a pain. He’s obviously just a 2A cosplay nerd.
0
0
14
@LinuxHandbook
Learn to shell script (bash or any other shell). Learn a scripting language like Python or Perl too… but that doesn’t replace all the knowledge you’ll gain about the system and system internals that you’ll gain by learning to shell script.
0
0
14
@carrickdb
I just use: E as in eye, I as in I, A as in aye, W as in write, G as in gnat, T as in tsunami, and so on.
3
1
13
Getting ready for London! If you're interested in
#OPSEC
, check out my BlackHatEU talk
#BHEU
@BlackHatEvents
0
5
13
Just finished a great discussion on Cyber Warfare in the 21st Century with
@pssi_prague
and
@CharlesUniPRG
. Many thanks to
@GOVCERT_CZ
and
@USEmbassyPrague
0
62
13
Standing room only to see
@BilyanaLilly
and
@sakkov
discussing foreign election interference at
@WarsawForum
1
3
13